If you deal with IT security or data protection – in short, information security – then you will stumble across DISA, CIS, ACSC and BSI quite quickly. We explain what the organizations and authorities behind these terms do and what they have to do with system hardening in particular.
DISA
The acronym DISA stands for Defense Information Systems Agency. This is the name of a U.S. agency that was subordinated to the Department of Defense. 1960 was the founding year of the Defense Information Systems Agency, which was called Defense Communications Agency until 1991. DISA has about 7,000 civilian and military employees, and its headquarters are at Fort Meade near Washington, D.C.

DISA deals with numerous military matters. These include, for example, the establishment of communications networks in crisis and war zones.
One of DISA’s divisions oversees the field of “cyber security.” In this context, the Defense Information Systems Agency publishes, among other things, the DISA STIGs – the Security Technical Implementation Guides. With these you can, among other things, carry out a professional Windows 10 system hardening and thus make your systems more secure against attacks.
CIS
The abbreviation CIS stands for Center for Internet Security. There is no authority or company behind it. Instead, the Center for Internet Security is an independent nonprofit organization that individuals and companies can join. FB Pro has also been a member for years.
The CIS was founded in 2000 and is based in East Greenbush (USA). The organization’s mission is: “Our goal is to make the connected world safer by developing, validating, and promoting contemporary best-practice solutions that help people, businesses, and governments protect themselves from pervasive cyber threats.”

The Center for Internet Security publishes the CIS Benchmarks, the CIS-CAT Pro and the CIS Hardened Images, among others. These benchmarks and tools can be used to harden systems such as Windows Server, among others.
BSI
The Bundesamt für Sicherheit in der Informationstechnik (Federal Office for Information Security), or BSI for short, is a German federal authority. It is part of the Ministry of the Interior (Bundesministerium des Inneren und für Heimat, the correct name) and is headquartered in Bonn.
Founded in 1991, the BSI had a budget of just under 170 million euros in 2021 and over 1,300 employees at two locations.

Small and medium-sized enterprises (known as SMEs) are advised by the Bundesamt für Sicherheit in der Informationstechnik, and it also serves as the central cybersecurity authority. Like many federal agencies, the BSI offers an extensive website: At bsi.bund.de, you can find news, advice and tips in the area of IT security.
Among the offerings are recommendations on how you can harden systems. One component is the study on system structure, logging, hardening and security functions in Windows 10, SiSyPHuS for short.
BSI’s tasks continue to include:
-
- Testing, certification and accreditation of IT products and services
- Warning of malware or security vulnerabilities in IT products and services
- IT security consulting for the federal administration and other target groups
- Information and sensitization of citizens for the topic of IT security and Internet security
- Conception of uniform and binding IT security standards
Development of crypto systems for federal IT - Function as a central reporting office for security in federal information technology and for critical infrastructures
ACSC
Australia also has an IT security authority called ACSC. The Australian Cyber Security Centre was founded in 2014 as the successor to the Cyber Security Operations Centre. It reports to the Australian Security Intelligence Organisation (ASIO), the “intelligence agency,” and the Minister for Defence.
Headquartered in the Australian capital of Canberra, the Australian Cyber Security Centre’s responsibilities include investigating cyber attacks and defending against them. Like the BSI, the ACSC issues advice and tips for companies to better secure their systems and IT infrastructures. This includes hardening guidelines.
Why are the authorities and organizations so important?
Information security is becoming eminently more important. Due to the advancing digitalization, hackers and other cyber criminals can access the data of companies and citizens in the worst case. This must be prevented at all costs!
BSI, DISA, ACSC, CIS and the like are on hand to help governments and businesses identify the threats and minimize the damage. One measure among many is hardening IT infrastructures and individual systems.
However, there is no one, ultimate solution! We have been working intensively on the topic of system hardening for a number of years and are constantly gaining new insights. For example, we took a look at the ACSC hardening recommendations and discovered some interesting “deviations” from other guidelines. You can find out what these are in our article “A look Down Under: What are the standards for system hardening in Australia?”
How do you perform system hardening according to the recommendations?
First of all, you need to determine the status quo of your systems. That is, how well are they hardened according to the standards?
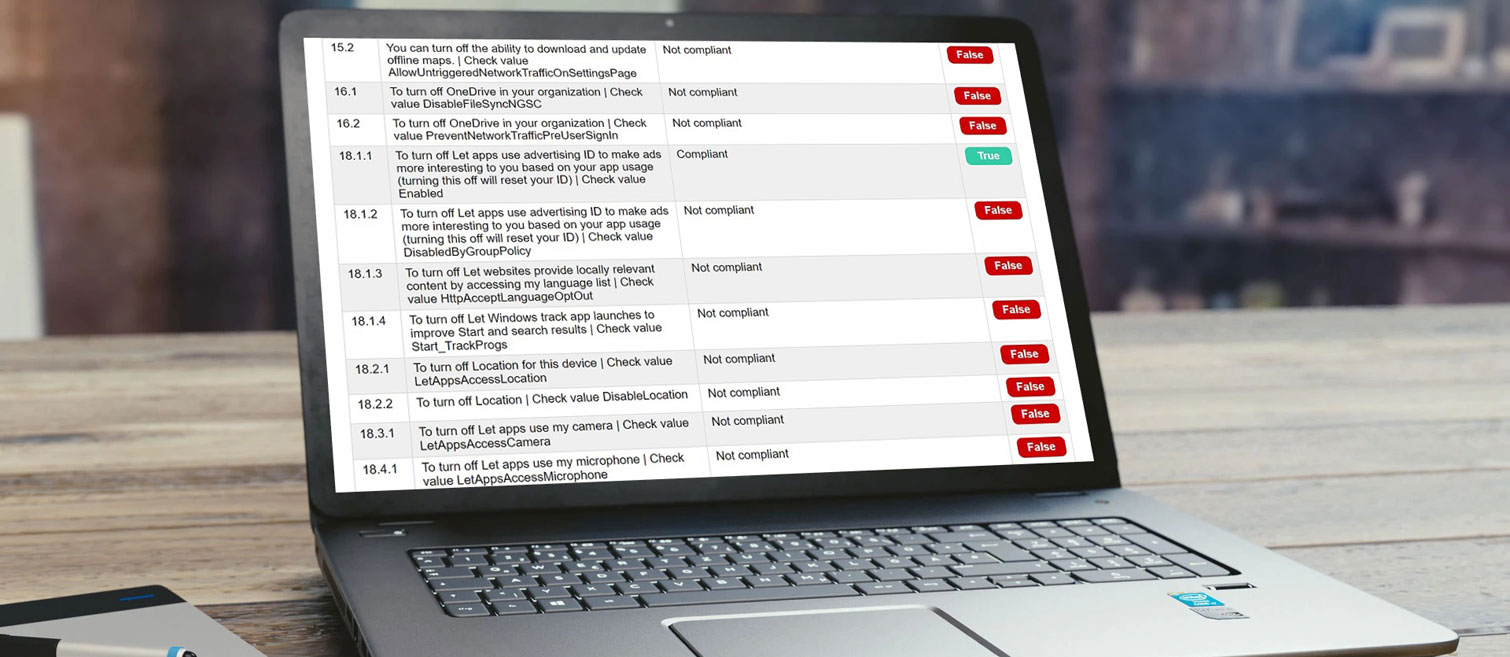
If you perform this check manually, it is extremely time-consuming! It is much faster with the free AuditTAP. Within seconds or minutes, you will receive a report that checks your applications (such as browsers and office applications) and operating systems according to BSI, CIS, DISA and ACSC standards.
If you know where there is room for improvement in your system hardening, you should address it as soon as possible. This measure also costs a lot of time, especially in large IT infrastructures, with “manual work”. That’s why it’s advisable to automate system hardening – for example, with the Enforce Administrator.
If you use our tools for automated hardening, a “self-healing system” is created in this way: Intentional or unintentional changes are detected and automatically rolled back in accordance with the specifications.
Do you need support?
Do you have questions about system hardening? Or do you need help with automated system hardening? Our experts are here for you! Contact us without obligation and we will get back to you as soon as possible.
Images: Pixabay, BSI, DISA, CIS
