To ensure that company-relevant information is protected in the best possible way, those responsible must rely on System Hardening, among other things. We explain exactly what this is here.
What does System Hardening mean?
System Hardening, simplified as Hardening, is the Secure Configuration of IT systems. The aim is to close security gaps and reduce attack surfaces for cyber attacks through various technical measures. By definition, Hardening is a preventive IT security measure. It serves to make both individual computers and large system landscapes more resilient.
What types of System Hardening are there?
In recent years, many specialised areas have developed. For example, there is OS Hardening, Endpoint Hardening and Software Hardening, dedicated Server Hardening, Linux Hardening, Kernel Hardening, Platform Hardening, Browser Hardening, SAP System Hardening, OT/IoT Hardening as well as the special Hardening of Space Systems.
What are the benefits of System Hardening?
Since highly sensitive information of a company as well as personal data are processed and stored on IT systems, the systems used must be subjected to special protective measures.
System Hardening is a very effective security measure. It secures the operating system, regardless of whether it is a physical, virtual or cloud-based system. In addition, applications such as office programmes and browsers are made more secure – for example, against data theft.
Sustainable System Hardening can significantly reduce the risk of a successful cyber attack. Furthermore, you can use hardening audits for anomaly detection, relieve the SOC team and forensic experts also work more efficiently thanks to System Hardening.
The bottom line is that Hardening protects critical corporate data and systems! If compromises occur here, extremely high damages are usually the result. In the worst case, your company will have to cease operations and file for insolvency.
How well are IT systems hardened “ex works”?
Common operating systems such as Microsoft Windows or Linux are configured by their manufacturers for the greatest possible compatibility and the broadest possible range of features. The systems are therefore equipped with potentially vulnerable components.
In other words, by default, operating systems do not apply restrictive security configurations. It is precisely these non-configured or often unused functionalities that attackers such as hackers often exploit as an attack vector.
During the hardening process at server or client level, such vulnerable functionalities as well as their exposed interfaces are deactivated or even uninstalled.
What threats exist without system hardening?
The main threats with non-hardened operating systems and applications include:
-
- Identity theft in the case of attacks on the central identity management structure
- Data manipulation of personal data and sensitive corporate data
- Data leakage such as copying entire databases
- Manipulation of applications or related systems
- Sabotage or espionage of operational and production processes
- Infiltration and distribution of malware
- “Data octopuses” collect detailed user data to create advertising profiles.
- Immense costs to eliminate the consequences of cyber attacks
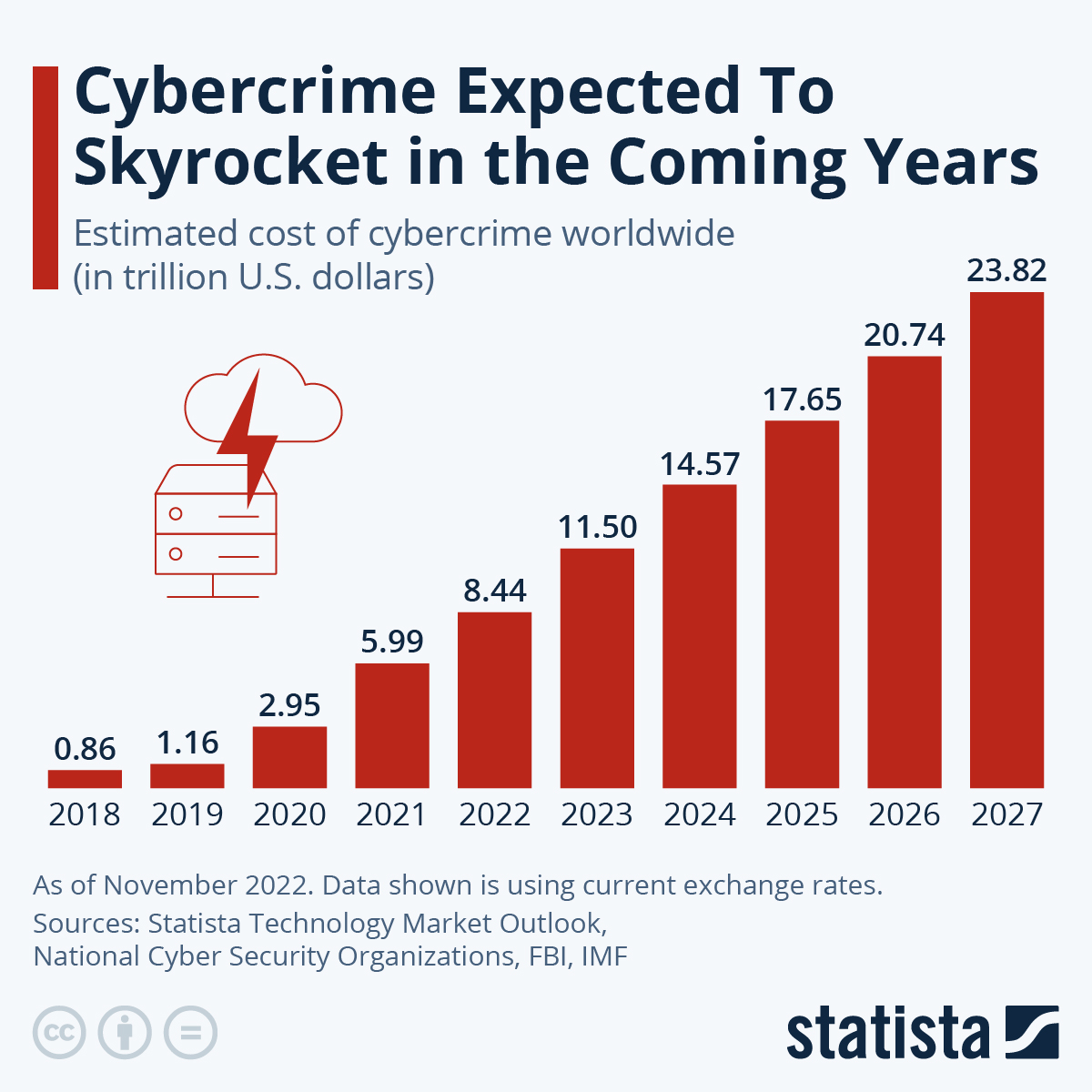
As various figures show, a large proportion of all companies are affected by hacker attacks, data theft and espionage. That is why information security and hardening of systems are extremely important!
Which companies need to deal with system hardening?
All of them! Regardless of whether it is a solo entrepreneur, a start-up, a medium-sized company or a corporate group: IT systems should be hardened in the best possible way everywhere. Because vulnerabilities can have serious consequences for any size of company.
The fact that the size of a company hardly plays a role in securing IT infrastructures is also shown by various new IT laws, regulations and standards. For example, System Hardening has been included in ISO27001:2022 and VDA ISA/TISAX. And the NSA and CISA also advise System Hardening.
Are you still not convinced? Then we have another argument: If you want to take out cyber insurance, you have to prove that you are properly securing your system landscape. Getting cyber insurance without proof of Hardening is becoming more difficult – or immensely expensive – by the day.

Extremely important: Hardening in the CRITIS sector!
The so-called cyber criminals stop at nothing and no one – certainly not at important sectors and critical infrastructures (CRITIS). These are even particularly at risk!
Therefore, CRITIS operators and similar organisations must secure their systems in the best possible way and according to the highest standards.
Hardening of systems: Important, basic measures
System Hardening is a technical building block to reduce possible weaknesses (“vulnerabilities”) of IT systems and IT infrastructures. The free handout from the german association TeleTrust recommends e.g. the following measures:
-
- Regularly review the necessity of activated services
- Operate running services only with minimal rights
- If possible: operate running services in an isolated environment
- Minimal assignment of rights for maintenance interfaces and accesses
- Restricted access to operating system configuration files
- Changing all existing default passwords with passwords according to an internal company password policy
- Disabling of:
- error or debug messages for end users
- unsafe, obsolete and/or unneeded interfaces
- unneeded autostart mechanisms
- unnecessary operating system components incl. background services.
- Activation:
- a screen saver with password protection
- strong user account control (UAC)
- the anti-virus programme during the boot process
- logging
- CPU security functions
- BIOS access password
- a fixed boot sequence
Recommended reading: You can get more advice in these articles:
Hardening servers: What should be considered?
TeleTrust says: “A large part of the hardening measures listed above is feasible through technical settings. These settings can be distributed automatically to all server systems of the company via a hardening package (for example by means of scripts).”
In addition, the following applies: New server systems should be provided with the appropriate standardised configuration directly after the installation is completed and exceptions to hardening should be managed centrally.
Recommended reading: Our guidebook “Hardening Windows Servers: Background, Measures and Tips” provides further information.
What should be considered when hardening Linux?
Linux and its numerous derivatives are sometimes very different from a Windows system. Therefore, many of the tips for System Hardening mentioned here are only applicable to a limited extent.
Nevertheless, Hardening is also extremely important for a Linux system, especially in the business environment!
Recommended reading: Useful advice can be found in our guidebook “Hardening Linux: System hardening for Ubuntu, Debian, Fedora & Co.”
Examples: How well does system hardening really work?
We have already investigated this question several times. Among other things, we tested two almost identical Windows 10 computers – as can be read in the article “Theory vs practice: What is the real benefit of System Hardening in field?“. There was only one difference: one system was hardened, the other was not.
Several checks, including with the HOLM Security Scanner, showed a clear picture. The hardened Windows 10 had significantly fewer vulnerabilities than a “normal” system.
But System Hardening is not only about the secure configuration of a complete operating system. Restricting individual services can also contribute to more data protection and privacy.
For example, in a test we found that an ordinary Windows 10 transmits numerous telemetry data to Microsoft. With a hardened system, this “radio traffic” is stopped. As a result, telemetry data no longer ends up with Microsoft and its partner companies. This means that you can stop “Windows spyware” through OS Hardening.
Hardening can also significantly reduce the danger posed by programmes such as Mimikatz or DefenderSwitch or DefenderStop.
Is there 100% system hardening?
In theory there is, but in practice it doesn’t make sense. If you configure your operating systems and applications so strictly that they are considered 100% hardened, you can only use them in a very limited way or not at all.
That doesn’t make sense. Therefore, you need to find a compromise between security and usability. You can find out how well you have managed this compromise by checking with AuditTAP.
The Risk Score of the AuditTAP report shows you how well you have hardened your checked system. Here is an example:

How well hardened are your systems?
Find out – with AuditTAP! The free tool automatically documents the configuration of your systems and compares them with the current BSI recommendations, CIS benchmarks and other proven standards.
How to install AudiTAP and quickly create a report with it can be seen in the following video. The clip shows how you can check, for example, to what extent your hardening complies with the BSI SiSyPHuS specifications.
Can System Hardening be automated?
Hardening IT systems is very complicated and, in large companies, also very complex. Normally, those responsible have to make thousands of settings manually. The measures therefore tie up a lot of resources (manpower, time, budget) that are needed elsewhere.
And: If you try to secure IT infrastructures via GPO or group policies, you get rather rigid and unsatisfactory results.
Nevertheless, the Hardening of IT systems must not be neglected under any circumstances! Otherwise, the likelihood of “cyber-gangsters” succeeding with their “cyber-attacks” increases.
How can an IT department reduce its time spent on System Hardening? Via automation! Self-created hardening scripts ensure that many system hardening processes run independently.
The monitoring of settings required in most compliance frameworks as well as the procedural integration (incident management, provisioning/deprovisioning processes, etc.) allow only one conclusion: automation of system hardening is without alternative!
Enforce Suite: The established hardening software
Developing and adapting automation scripts also takes time. To reduce this effort, the #NoCodeHardening initiative was born. The association of several IT companies, which also includes FB Pro GmbH, is advancing hardening automation through powerful hardening tools for companies. Among other things, a comprehensive software solution was developed for this purpose: Enforce Administrator.
Enforce Administrator: Get detailed information!
With Enforce Administrator, state-of-the-art hardening configurations can be created, deployed on IT systems and also managed centrally and transparently during the life cycle of an IT system, as well as documented in a traceable manner.
Conclusion: What are the pros and cons of System Hardening?
On the pro side, System Hardening increases the overall security of the system, making it more resilient to unauthorised access and potential cyber threats. But implementing hardening measures can be complex and require specialised knowledge. And System Hardening requires ongoing reviews and updates to adapt to evolving threats.
Need more information?
Our experts will be happy to advise and support you in auditing and hardening your IT systems according to the latest standards and specifications.

