As part of their monitoring obligations, our customers and partners regularly ask for proof of information security, for example in the form of an ISO27001 certificate.
At present, the cost of introducing an information security management system based on ISO27001 is not commensurate with the benefits.
In order to nevertheless meet the justified demands of our customers and our own high expectations, we have decided to implement technical and organizational measures (TOMs) on the basis of the CIS Controls.
The CIS Controls
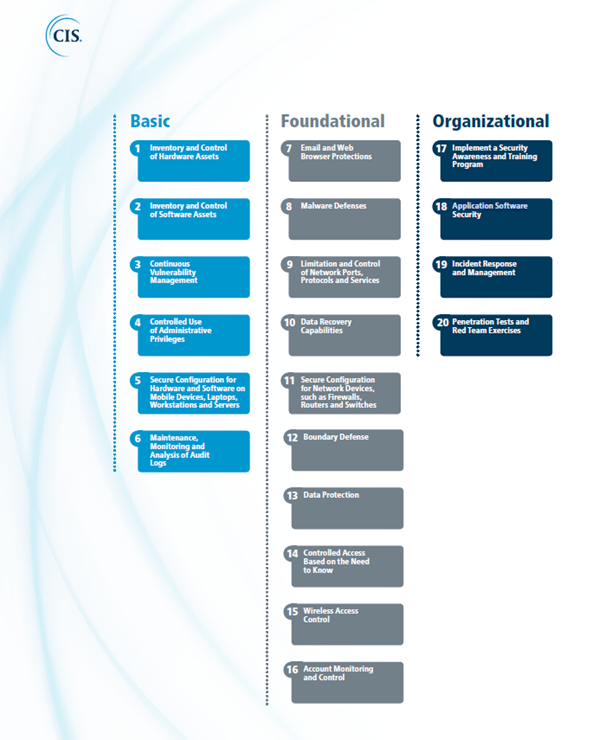
The so-called “CIS Controls”, published by the “Center for Internet Security” define prioritized measures to protect corporate data and relevant information from known cyber attack vectors.
The CIS Controls are publicly available, regularly updated and are recognized as compatible with ISO 27001. The CIS Controls are divided into the following three categories:
-
- Basic
- Foundational
- Organizational
The figure below provides a clear overview of the structures:
Transmission of our technical and organizational measures
In the context of customer projects, we will be happy to provide you with our technical and organizational measures following the conclusion of corresponding confidentiality agreements.
Further questions?
Do you have further questions about the implementation of our technical and organizational measures?