More and more OT devices are connected to networks and internet. This heavily increases the risk of cyber attacks. This is how System Hardening and other security measures improve OT security.
Definition: What is Operational Technology?
Operational Technology (OT) includes hardware and software used to control and monitor systems and devices. OT is frequently used in manufacturing industry, in construction industry and in energy sector – and thus also in critical infrastructures (CRITIS).
Evolution: From OT and Edge Computing to IoT and IIoT
In the past OT systems often were isolated. That means, “isolated applications” were not connected to networks or internet. In the context of digitalization, networking is increasingly taking place. This offers these advantages, among others:
-
- Devices collect and process important data to centrally control machines and plants via SCADA (Supervisory Control And Data Acquisition).
- Collection of large volumes of data (keyword: Big Data) in conjunction with data analyses makes it possible to design processes more efficiently.
- Connected devices also support “Predictive Maintenance”.
- And Edge Computing means that all data collected no longer has to be sent to a central data center, which saves time and resources.
Networking OT devices thus leads to “Internet of Things” (IoT) or the “Industrial Internet of Things” (IIoT). These components help companies on their way to digital transformation towards Industry 4.0.
But connecting all these devices, a new, very big problem arises: systems are “online” and thus vulnerable to internet based attacks.
Security: OT security is a major challenge
If a device is “offline” and not connected to (public) networks, many attack vectors are eliminated. One only has to make sure that it is protected physically and digitally by access restrictions. If networking is to take place, a DMZ (Demilitarized Zone) is a good way to provide basic protection.
But this is not the end of the story! In modern OT security, companies should take multiple measures to properly protect their OT and IoT/IIoT systems. This is especially important for companies and organizations in the CRITIS sector.
For example, to reduce rising cybersecurity risks while meeting increasing regulatory requirements, vulnerability scanners, SIEM (Security Information & Event Management) and MDR (Managed Detection & Response) systems must be implemented. In addition, penetration tests and IT forensics help to find hidden security vulnerabilities.
System Hardening: an essential part of OT security
Most measures to secure OT systems are in the areas of “detection” and “response”. Although these measures detect attacks and, in the best case, prevent them, are purely reactive. It is much better to greatly reduce the attack surface. Because: a small attack surface reduces the risk of successful cyber attacks!
Preventive protection (i.e., System Hardening / Secure Configuration) combined with appropriate response capabilities (detection and response) should be the strategy!
System Hardening belongs to the area of preventive measures. In the NIST CyberSecurity Framework or in ISO 27001, this is the “protection” domain. Here, OT devices are configured on the basis of industry-proven standards so that they are considered securely configured (“hardened”).
Hardening is achieved, among other things, by switching off services that are not required and by restricting access rights. In this way many attacks and other compromise attempts come to nothing. Why? Because the technical vulnerabilities that are usually exploited in attacks are simply no longer available.
Important: System Hardening is not a one-time, selective measure! It is extremely important that hardened OT devices are permanently monitored, configurations are optimized and operating systems and applications updated. This is the only way to keep systems up to date with state of the art techniques. This applies to all OT systems, especially in critical infrastructures!
Sustainability: How can OT systems be permanently hardened?
Hardening IT systems is very complicated and, in the case of large system landscapes, also very complex. Normally, project or IT managers have to manually configure hundreds or even thousands of settings. In addition, it is necessary to monitor the hardened OT devices in case settings are changed accidentally or deliberately.
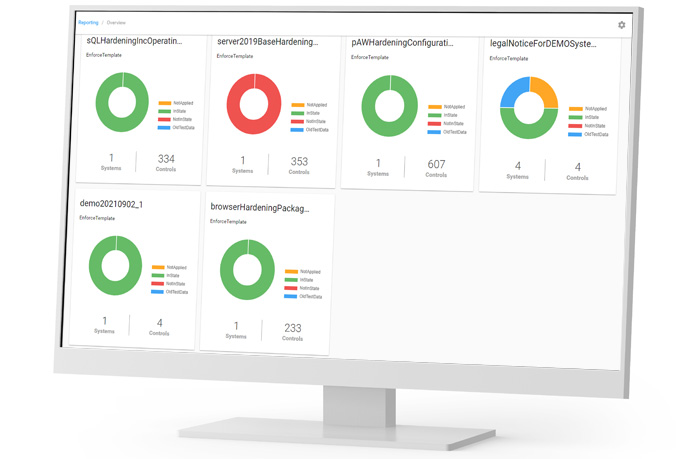
To conserve already scarce IT and OT resources, it is advisable to introduce automated System Hardening. Hardening tools such as the Enforce Administrator configure a kind of “self-healing system” in which many attack vectors are disabled and can thus no longer be exploited.
System Hardening works reliably. This is proven by our customer HUBTEX, among others. In this success story, you will learn how we used our Enforce Suite solution to securely configure OT components for use in the CRITIS environment:
Wie HUBTEX seine Spezialfahrzeuge sicher für einen KRITIS-Einsatz macht
Check: Do you know how well your systems are hardened?
No? Then perform a check with the free AuditTAP. The AuditTAP modules check various standard products for the configuration of important and relevant security settings. The references checked against are fundamentally established and proven security standards.
If you have any questions about System Hardening or need support, please feel free to contact us at any time without obligation. Write us an e-mail for this purpose.
Image: Freepik

