DIN EN ISO 27001:2022 defines numerous aspects of information security. One important aspect required in the new version is secure system configuration – also known as system hardening. Here’s what you need to know about it.
Note: We are constantly updating and adding information to this article
Last update: June 2023
[lwptoc depth=”1″ title=”Table of contents:”]
Definition: What is DIN 27001?
DIN EN ISO 27001 or DIN/IEC 27001 – as the full name is written – is a standard that is recognized worldwide. It describes how information security management systems (ISMS for short) are to be designed in order to better ward off cyber attacks and adequately protect companies’ information assets.
On 10/25/2022, the final version of ISO 27001:2022 was published.
How are ISO 27001 and ISO 27002 related?
ISO 27002 is a guide that describes specific controls and measures for implementing the ISO 27001 ISMS. The standard provides detailed guidance for selecting, implementing, and managing information security controls in organizations.
ISO 27002 is based on Annex A of ISO 27001 and uses the same control designations. However, ISO 27002 provides a more detailed explanation of the controls and includes practical recommendations for their implementation.
How do ISMS and system hardening go together?
An information security management system is the establishment of guidelines, processes and procedures within an organization. These are used to permanently define, manage, control, maintain and continuously improve information security within a company.
System hardening serves to reduce the attack surfaces of IT systems. This is done, among other things, by disabling services that are not required. The configuration of log and audit settings is also part of hardening. Because: If the worst comes to the worst, you want and need to be able to trace how a possible attacker has proceeded (“IT forensics“).
Secure System Configuration should be based on established and proven standards. Such recommendations are defined and published, for example, by authorities and organizations such as CIS, DISA, ACSC, BSI and companies such as Microsoft.
This means: System Hardening has been an elementary component of an ISMS since the update of the “normative reference”!
Content of ISO 27001: What exactly changed in the new version?
ISO 27001:2022 brings with it a number of adjustments and innovations. Here is an overview of the most important changes from our point of view.
Changes to the controls
The updated standard recognizes eleven new measures (“Controls”). They are:
Threat Intelligence
This Information Security Standard is used to put a threat into context or to help identify and detect threats.
Information Security for use of Cloud Services
When cloud services are used, information security must also be addressed.
ICT Readiness for Business Continuity
The requirements for the IT landscape should be derived from the perspective of the business processes.
Physical Security Monitoring
Appropriate measures must also be defined and monitored to prevent unauthorized access and physical access (buildings, hardware, etc.).
Information deletion
Deletion concepts ensure that data is deleted in compliance with data protection requirements.
Data Masking
Various masking techniques such as anonymization and pseudonymization increase data protection.
Data leakage prevention
Measures in this field prevent unintentional data leakage.
Monitoring Activities
Network and application behavior are monitored with the aim of detecting anomalies and taking appropriate action.
Web Filtering
Access to external (insecure) websites must be restricted. After all, not every website needs to be accessible from a corporate network.
Secure Coding
In software development, special measures help to develop comprehensibly secure code.
Configuration Management
Secure configuration (“System Hardening”) occupies an important place in the updated standard. This is shown, for example, in this overview:
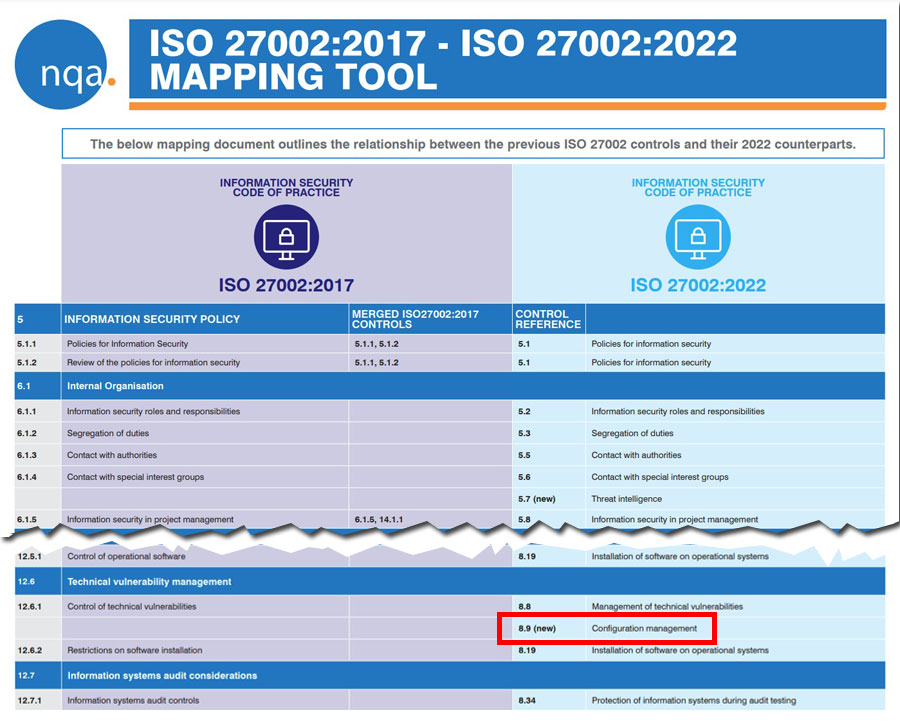
Note: An overview of the similarities and differences between the “old” ISO 27002:2017 and the “new” ISO 27002:2022 is available in this PDF from NQA.
Changes to the structure
All controls are reassigned to four categories:
-
- Organizational measures (37 controls)
- Personnel measures (8 controls)
- Physical measures (14 controls)
- Technological measures (34 controls)
Changes to attributes
Attributes are a means of categorizing measures. They allow controls to be quickly compared to industry standards. It follows:
Control Type
Effect of the control or measure
Information Security Property
Which of the classical goals of information security is supported (confidentiality, integrity and availability)?
Cybersecurity Concepts
Integration and assignment in security frameworks
Operational Capabilities
Operational capabilities of the organization
Security Domains
NIS Security Domains of ENISA
Each measure now has a table with a set of suggested attributes. Annex A of ISO 27002:2022 contains a set of recommended links.
Where does System Hardening play a role in the new standard?
System Hardening, or the secure configuration of IT systems, plays a key role throughout the revised DIN EN ISO 27001 (Version 2022).
In the “Configuration Management” control, which also includes “Secure Configuration Management”, requirements are placed on secure configuration (“hardening”) on several dimensions.
Here is a simplified overview:
“Templates” are to be used. This eliminates the need for self-developed hardening configurations.
Process requirements: A structured process for implementation is to be applied.
“Monitoring” of the configuration is also required; changes and deviations must be identified.
What does not sound so comprehensive in the first step, leads in our view to the fact that known methods such as group policies should no longer be used. Why? Counter question: How exactly is “monitoring” of various hardening configurations implemented on hundreds or thousands of IT systems?
Protect – Detect – Respond: Why do you have to think of everything?
What is particularly important: The adapted standard clearly addresses the fact that there are differences between implicit and explicit protective measures (“protection”) and detection and response (“detection and response”). Differences that are often not so clear and companies therefore implement some measures very often in the “detect & response” sector. From our point of view, however, protection starts much earlier – why not simply “configure away” vulnerabilities?
Established standards see it similarly – the NIST Cyber Security Framework defines five critical functions, shown below as a diagram:

If one assigns the measures “identify”, “protect”, “detect”, “respond” and “recover” to the priorities of IT security managers and/or decision-makers, it quickly becomes clear: people often rely exclusively on the detection of malware and cyber attacks. The associated reaction (“respond”) is often less well defined – the field of prevention is often treated stepmotherly in reality.
This means that those responsible are very much concerned with the detection and elimination of malware and intruders. But hardly any time is spent on actually protecting systems through a sensible, standardized and comprehensive security configuration of IT systems.
As a result, security gaps in operating systems and applications remain, and all that is installed is a “bouncer”.
Can the requirements of ISO 27001 be met in this way?
From numerous discussions with information security and IT managers, we know that in the overwhelming majority of german companies, the field of “detection and response” is nevertheless currently at the top of strategy papers and investment plans.
Vulnerability scanners, SIEM and MDR solutions, anti-malware suites and the like make sense – definitely! But from an IT security perspective, the focus is too much on “detection & response”. This is no way to meet the increased requirements of ISO 27001:2022!
Measures in the area of “protection”, i.e. the protection of endpoints, IT systems, notebooks and servers, are necessary and will now have to be demonstrably delivered as part of the annual audit.

What needs to be done now?
Every company that faces the re-certification of the (then also new) DIN EN ISO 27001 in the annual rhythm must now start to raise the topic of “System Hardening” to decision-maker level. Because the auditor will ask for corresponding processes, measures and evidence in the next meeting – and even if you initially still refer to the transition periods. The topic can no longer be discussed away!
To set up and implement the comprehensive protection concept, you need a secure and permanent configuration of your IT systems. You can do this with special hardening tools. These include programs such as AudiTAP (for checking systems) and Enforce Administrator (for implementing sustainable, automated hardening).
Do you need help with the secure configuration of systems?
Do you have questions about automated System Hardening? Do you want to integrate System Hardening directly into your deployment or installation processes? Our experts are here for you! Contact us without obligation and we will get back to you as soon as possible.
Images: Freepik, NIST, FB Pro
