We are often asked why we do not carry out System Hardening on the basis of Group Policies or Group Policy Objects. The quick answer: Because the handling is massively inefficient and the results are therefore unsatisfactory! We explain why this is the case in this article.
Group policies: useful and important
Group Policy Objects (GPO) were a great thing at the time of their introduction – around 25 years ago (ActiveDirectory with Windows NT/2000). They represented a big step forward, as administrators came closer to the goal of achieving a uniform configuration on remote or distributed systems with little time expenditure.
Meaningful Group Policies were easy to create back then. Even today, GPOs are a popular and widely used tool for distributing and maintaining configurations.
Important GPOs such as the Default Domain Policy usually contain company-wide settings for password configuration for “domain-integrated” user accounts.
However, it is becoming increasingly apparent that Group Policy Objects lack important functionalities or do not focus on them. These include sensible Group Policy management, monitoring and auditing of settings, comprehensive or role-oriented configurations and standardized and infrastructure-wide reporting. This will not change much in the future.
In this article, for example, Microsoft itself explains the advantages of newer technologies such as PowerShell DSC over GPOs.
Can system hardening be done via Group Policy?
Yes, in principle GPOs can be used technically to distribute system configurations and therefore also hardening settings.
For example, you have the option of following the SiSyPHuS specifications of the German Federal Office for Information Security (BSI). To do this, download the Group Policy Objects for hardening Windows 10 and then transfer a hardening configuration to the target systems on a GPO basis. The Center for Internet Security (CIS) also provides group policy-based configuration sets.
However, there are weighty arguments against implementation via GPO:
| ❌ | In addition to the high manual configuration and, above all, documentation effort (initial and ongoing), there are also massive practical implementation hurdles. |
| ❌ | Non-domain-integrated systems must be considered separately (DMZ, cloud-based systems, backup systems, production/OT environments). GPOs managed centrally in ActiveDirectory do not work here. |
| ❌ | Linux-based systems must also be considered separately. |
| ❌ | With their recommendations, many hardening specifications from CIS, BSI & Co. go beyond the technical possibilities that can be mapped using the “standard” GPOs. |
| ❌ | Additional technical configuration options (PowerShell etc.) must therefore be used or separate ADMX templates created, which massively increases the complexity and effort required for documentation. |
| ❌ | GPO settings are not always applied to the target systems. With hundreds of servers or clients, who checks whether the settings are actually applied? |
| ❌ | OU structures often contain computer objects that are no longer up-to-date. An initial clean-up is therefore also required here due to the lack of restore options. |
In a constantly changing world of (cyber) threats, the question therefore arises as to whether you should really still rely on “rigid” GPOs in the area of IT security. This is because, as explained in the introduction above, eminently important functionalities are missing for meaningful Security Configuration Management (SCM)!
Do you have any questions? Contact us!
Security Configuration Management via GPO: the advantages and disadvantages
In the following table, we have summarized what we consider to be the relevant advantages and disadvantages of GPO-based System Hardening:
| Advantages | Disadvantages |
| The Microsoft baselines can be downloaded free of charge | Deep know-how about configurations is needed |
| Since the baselines are delivered as GPO, they can be applied directly | Since the baselines are delivered as GPO, they can be applied directly |
| No special infrastructure is required for the application | Configurations for GDPR / DSGVO topics are to be developed by yourself |
| No additional licenses need to be purchased | Settings are to be adapted independently to newer versions of hardening frameworks |
| The technology is well known and successfully million times in use | A simple rollback of the settings is not possible, “inverted” GPOs are necessary |
| There is no central control and reporting facility, only individual evaluations | |
| A hardening configuration cannot be further processed in third-party systems, because no interfaces exist | |
| For systems not integrated in AD, special paths are necessary to apply GPOs | |
| The extensions to the MS Security baselines must be made manually |
In other words, System Hardening via Active Directory and Group Policy is a monolithic solution. One that requires a lot of manual work – which heavily loaded IT departments have a hard time doing.
Add to that the fact that OS Hardening must be done, monitored, and adjusted on an ongoing basis! Otherwise, gaps quickly develop that data octopusses, hackers and “cyber gangsters” can exploit. The consequences can be expensive and even threaten the existence of your company.
How can sustainable System Hardening be realized?
If you only have a few systems, for example a few workstations and servers, hardening via GPO may be fine. The effort required for implementation, monitoring and adjustments is considerable, but feasible with a well-staffed IT team.
However, genuine, in-depth and sustainable System Hardening with all aspects of Secure Configuration at a high level cannot be achieved in large IT landscapes with GPOs – at least not at a reasonable cost.
There is only one sensible solution: automation!
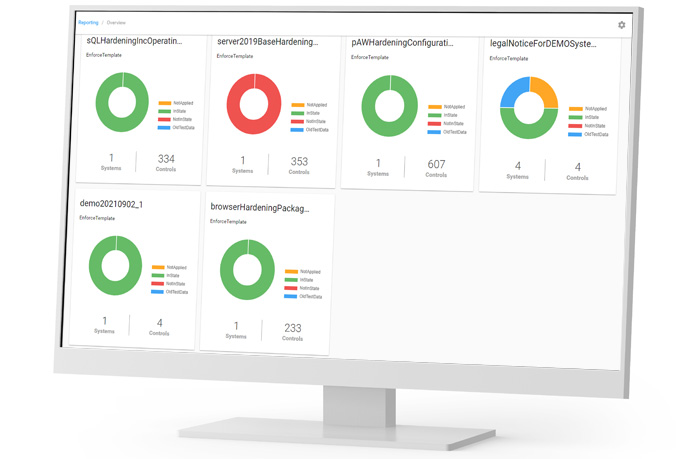
Various solutions are available for automation, including the Enforce Administrator. With the Enforce Administrator, automated System Hardening is carried out on the basis of proven and current standards.
Also integrated: A systems management and audit system for monitoring the compliance status. Regular “self-healing” based on the defined configurations is also included.
Enforce Administrator: Get more information
GPO versus Enforce Administrator: the comparison
In which areas do Group Policies score points? And in which aspects is a professional hardening tool like Enforce Administrator the better choice? You can find the answers here:
| Features | Group Policy Objects | Enforce Administrator |
| Opportunity to set an innovative, company-wide standard | Yes | Yes |
| Simple, role-based management of diverse hardening configurations | No | Yes |
| Automatic correction of non-conforming settings | Yes | Yes |
| Detection of non-conforming settings | No | Yes |
| Automation via REST API and integration with third-party systems | No | Yes |
| Simple web interface for configuration | No | Yes |
| Merging of several hardening recommendations into one configuration | No | Yes |
| Risk minimization by avoiding permanent (local) admin rights | No | Yes |
| Permanent monitoring and alarming function | No | Yes |
| Easy creation of reports, e.g. for compliance and DSGVO audits | No | Yes |
| Entry and Time to Result | High | Low |
| Restore old configurations | High effort | Low effort |
Conclusion
Group Policies and Active Directory were and are a great thing. But when it comes to Security Configuration Management, GPOs quickly reaches their limits. This is because SCM requires process integration, detection options and monitoring in addition to the actual implementation of a secure configuration.
To compensate the limitations, an extremely large amount of time would have to be invested in manual activities. However, the current shortage of skilled workers does not allow this in almost any company.
For sustainable System Hardening, SCM needs to be automated – at all levels: setup, monitoring, and customization. This is the only way to keep IT infrastructures compliant with current recommendations and standards in the long term and effectively reduce the risk of successful cyber attacks.
If you need support in this regard, please feel free to contact us.
Images: Freepik Pikaso, FB Pro
