Do you know how OS Hardening works? We give you an overview of the topic and answer the most important questions in FAQ style.
What is OS Hardening?
“OS Hardening” stands for “Operating System Hardening”. This is a measure in the field of IT security or cyber security to make operating systems such as Windows or Linux more secure against cyber attacks. OS hardening is thus a component of the more comprehensive System Hardening.
How does OS Hardening work?
In Operating System Hardening, you identify vulnerabilities in the operating systems used, for example on your workstations and servers. In the hardening process, you try to close gaps that can be exploited by attackers or “data octopuses” as best as possible. They do this by applying special OS Hardening techniques and measures.
What OS hardening measures/techniques are there?
Basically, it is about configuring your operating system in such a way that it offers as few vulnerabilities and attack surfaces as possible. To do this, you disable services that are not needed, deactivate ports, uninstall outdated programmes, restrict user rights and activate update services. Taken together, these are several hundred settings per system.
Important: Your respective measures depend on the operating system. A Windows 11 hardening differs only slightly from a Windows 10 system hardening, but the hardening of a Windows Server system has a few special features. Linux hardening, for example, is completely different – not only because there are dozens of distributions, including Ubuntu, Fedora and others.
Examples of hardening an operating system
To effectively harden your operating system and raise information security to a higher level, you should take the following measures, among others:
Remove or disable unnecessary services
Many operating systems have services activated that are not required for daily operation – or even highly dangerous. By deactivating or removing these services, you reduce the attack surface of your system.
A well-known example: the “Eternal Blue Exploit” via the SMBv1 protocol.
Configure your firewall
Set up your firewall carefully to block unwanted access while allowing legitimate traffic.
Implement access controls
Ensure that only authorized users have access to the systems. And limit their authorizations to what is absolutely necessary.
Use authentication mechanisms
Introduce guidelines for strong passwords and use multi-factor authentication to increase security.
Encrypt data
Protect both data at rest and data in transit with modern, secure encryption to ensure its confidentiality and integrity.
What distinguishes OS Hardening from other cyber security measures?
With System Hardening in general and Operating System Hardening in particular, you figuratively lock the doors to your IT system landscape. This makes it much more difficult for attackers to penetrate and compromise workstations, servers and networks.
With this approach, OS Hardening is one of the preventive measures in the IT security triad (“Protect – Detect – Respond”). This clearly distinguishes it from many other solutions. These are usually located in the areas of “Detect” and “Respond”.

Operating system hardening is an important IT protection measure that is increasingly required by laws, regulations and organisations. For example, hardening has been included in ISO27001:2022, NIS2, DORA and VDA ISA/TISAX as a fundamental measure.
More and more cyber insurers also expect their customers to implement OS hardening, among other things – otherwise there are no policies or severely limited benefits in the event of a damage claim.
Are there standards for operating system hardening?
Yes, organisations such as CIS, DISA and ACSC have been issuing recommendations for hardening operating systems for years. Microsoft also regularly publishes OS Hardening checklists and guidelines.
Even US authorities such as the NSA (National Security Agency) and CISA (Cybersecurity and Infrastructure Security Agency) publish so-called Cybersecurity Advisories for OS Hardening.
Does automation help to “harden” operating systems?
Yes, definitely. If you configure an operating system securely by hand, you have to make at least 300 to 500 settings. Depending on the strategy and goal, that can be as many as 1,000 configuration changes – on one computer alone!
In large IT landscapes with dozens or even hundreds of systems, OS Hardening alone “eats up” gigantic resources. Resources that are usually scarce in IT departments.
Automation is therefore a (necessary) duty. If you use professional hardening tools for companies, you can save a lot of time. For example, AuditTAP can be used to do a quick Hardening Audit. This check shows whether your operating system is hardened according to various standards or not.
If you know how well or poorly a single operating system or several operating systems are hardened, you should take appropriate measures as quickly as possible. Here, as already mentioned, automation can help enormously, as it makes the secure configuration (in parts) traceable and above all reproducible.
Is that not enough for you? You can get fully automated “all-round protection” with Enforce Administrator, whose strength lies in OS Hardening of Windows 10/11 and server systems (Windows and Linux).
Enforce Administrator: More Informationen
What is the goal of OS hardening?
When you harden an operating system, you want to secure it as best as possible against hackers, ad networks or data brokers and cyber criminals. The goal of OS Hardening is to close as many gaps and other potential sources of danger as possible in order to significantly reduce the attack surface.
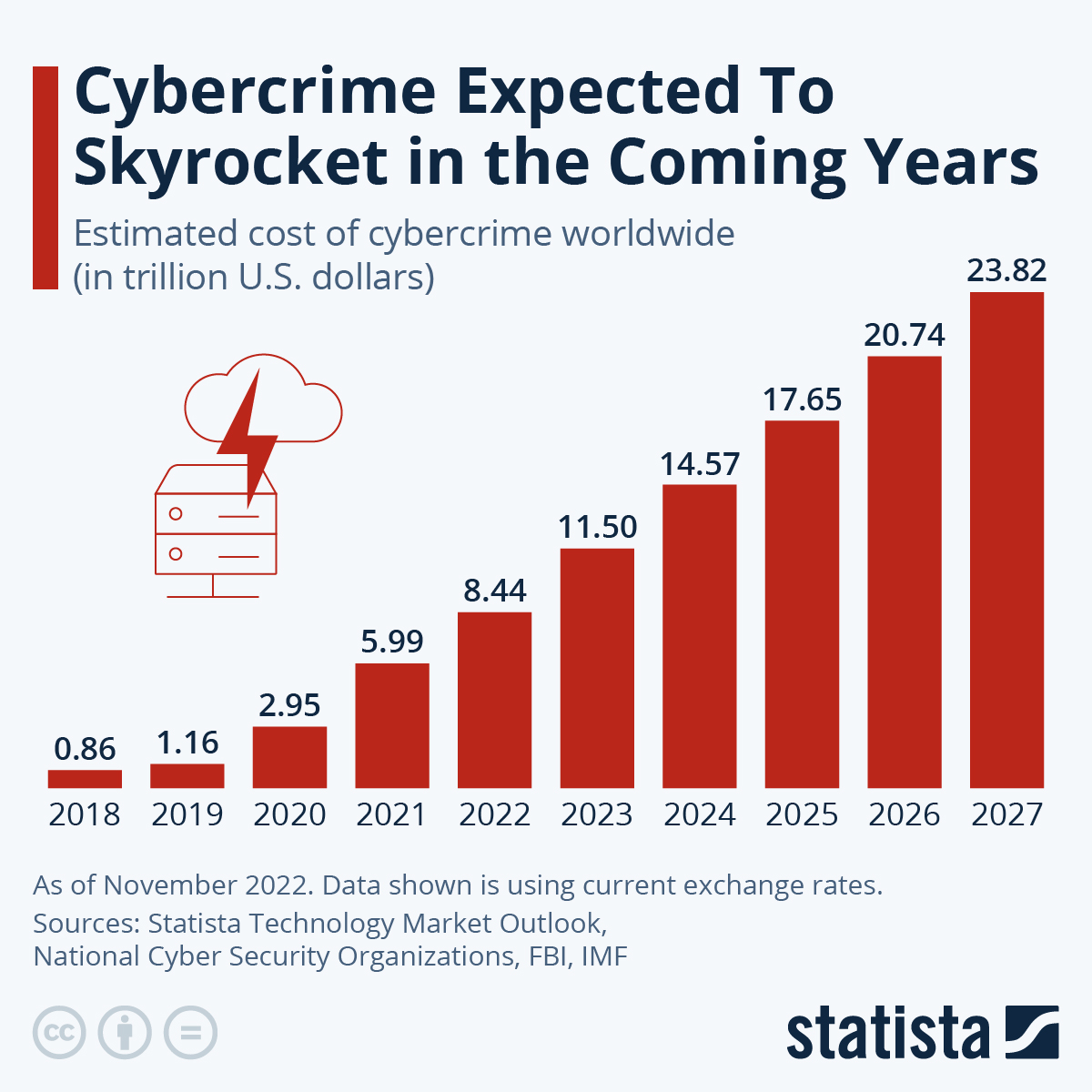
With professional Operating System Hardening, you reduce the risk of your company falling victim to data theft, espionage or sabotage through cyber attacks. And in doing so, you reduce the risk that your company will have to bear the costly and possibly existence-threatening consequences of a data breach, for example.
Do you need help or support with OS Hardening?
Would you like to know more about OS Hardening? Do you need hands-on support? Or would you like us to help you introduce the Enforce Administrator? Simply get in touch with us.

