The detection of anomalies is an important measure in IT security. In order to be able to implement this correctly, there are various approaches and solutions.
[lwptoc depth=”3″]
What are anomalies?
By definition, anomalies are unexpected deviations or irregularities from a normal or standard state. What is considered a normal state must be defined beforehand.
To detect deviations from the normal, IT usually relies on anomaly detection systems. These help to detect unusual patterns.
Examples of anomalies in IT systems
Unknown or noticeable deviations can be:
-
- Increased (or “different”) traffic on a network or website
- Unknown or changed data packets
- New network connections that are not in a “normal” state
- New devices or users on a network
- Traffic over unusual protocols
- Unauthorised scans of systems
- Strange or unknown error messages
- Unauthorised installation of applications
- Changes to configuration settings
- Deactivation of security functions
As you can see: Many anomalies fall within the scope of network anomalies, but there are also numerous “mysterious” changes at the local level – for example, on single-user computers. Therefore, it is important to look at the topic of “anomaly detection” holistically.
How does anomaly detection work?
Never act on a gut feeling alone!
To recognise deviations from a normal state, the normal state must first be defined. To do this, define key figures that can be clearly measured over a long period of time. In addition, you should define threshold values at which the normal range is left and one can speak of an anomaly.
In IT, it is common to automate anomaly detection using various methods and systems. Among other things, measurements are taken regularly and log files are analysed.
One problem with anomaly detection can be the flood of messages. False positives, i.e. false alarms, are often the cause of this. Therefore, on the one hand, it is important to ensure that as few incidents as possible occur. On the other hand, you need a solution to filter out the really relevant ones from the flood of false alarms.
Why is anomaly detection so important?
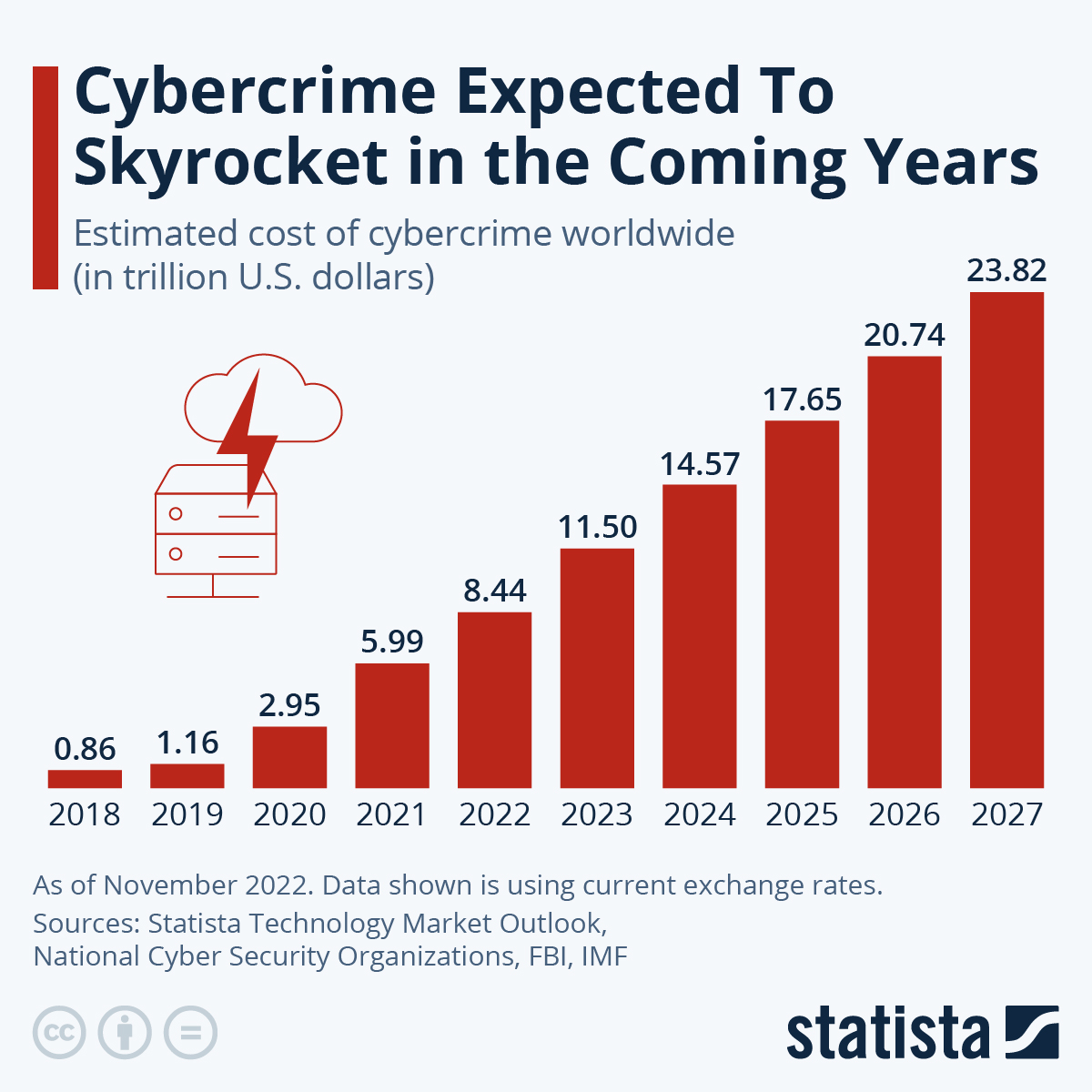
Anything that deviates from a norm can be dangerous. In the medical field, an anomaly could indicate a serious illness; in the IT field, cyber-attacks may be the reason for irregularities.
With professional anomaly detection you can, for example, identify weak points in your network or successful hacker attacks. When the alarm bells start ringing, you should take countermeasures as soon as possible! If you do not have any processes or systems in place for anomaly detection, you are virtually blind: you do not even notice when cyber gangsters break into your IT infrastructure or IT systems, spy on your company or steal data.
This “blindness” can be costly in several ways: Secret information may be leaked and there is a loss of image when the data breach becomes known. In addition, there may be hefty fines because you have not properly secured your infrastructure, which is required by law in many areas.
Are there laws and standards that require anomaly detection?
Yes. For example, the German IT Security Act 2.0 require that companies in the CRITIS sector (critical infrastructure) in particular must use special systems to detect attacks. Among other things, these systems have to detect and log anomalies.
In addition, ISO 27001 is establishing itself as a certification standard in many sectors and industries. Within this framework, you must establish an ISMS (Information Security Management System). This must include anomaly detection, for example.
Other rules and regulations such as VDA-ISA, TISAX, BAIT or VAIT require state-of-the-art IT security measures and systems. This also includes an anomaly detection solution.
Which anomaly detection systems have been established?
Since there is not _the_ anomaly, there is accordingly not _the_ anomaly detection system. In recent years, various concepts and solutions have become established in the field of information security. For example, these:
-
- IDS: Intrusion Detection Systems
- SIEM: Security Information & Event Management
- SEDM: Security Event Detection Management
- MDR: Managed Detection & Response
- XDR: Extended Detection & Response
Hardening audits can also be included in the area of anomaly detection.
How do anomaly detection and System Hardening go together?
The Secure Configuration of applications and operating systems, so-called “hardening”, ensures that there are fewer attack surfaces. Because – to put it simply – where there is no vulnerability, there can be no misuse. Accordingly, System Hardening also ensures that fewer anomalies and false positives are reported. The SOC team is thus massively relieved.
In order to harden your systems effectively, you need to conduct regular audits. These allow you to identify weak points and optimisation potential. Such a check can be easily carried out with the AuditTAP. AuditTAP detects unusual settings and points them out.
Would you like to check your hardened systems permanently and automatically? Then you should use the Enforce Administrator. The hardening tool for companies offers numerous functions, one of which is anomaly detection.
This means that if a configuration is changed in your system landscape – by mistake or through cyber attacks – Enforce Administrator recognises this intervention and reverses it independently and can start appropriate escalation levels. This creates a kind of “self-healing system” with complete control.
Does machine learning make anomaly detection better?
Algorithms based on machine learning (ML) or other forms of artificial intelligence (AI) can make an anomaly detection system better. They ensure that changes are detected and attributed more quickly. The number of false alarms thus decreases – sometimes significantly.
Conclusion: Do companies need anomaly detection systems?
Yes, definitely! In order to be able to comprehensively protect IT systems, the triad of “Protection”, “Detection” and “Reaction” is needed. Methods and systems for anomaly detection fall into the area of “Detection”, System Hardening into “Protection”.
Both are closely intertwined. Because something that is very well protected (i.e. sensibly and securely configured) generates few anomalies.
Do you have questions about System Hardening? Do you need support in developing a sustainable hardening strategy? Or would you like to implement a solution like Enforce Administrator in your IT processes? Contact us!
Image: Adobe Firefly

