Does System Hardening really achieve anything? Do the IT security measures really close many security gaps? How can you measure the results? And is a 100% hardening even possible? We provide you with some deep insights and verifiable facts here.
Test round 1: How well does System Hardening really work in ‘standard operating systems’?
Are standard systems ‘ex works’ configured securely? And what are the benefits of subjecting systems to System Hardening? We pursued these questions with a series of tests. We carried these out both alone and with our partner Trovent.
Our colleagues at Trovent are experts in the areas of Penetration Testing, Managed Detection & Response and Forensic Appliance, among other things. They therefore supported us with the compliance scans. To do this, we first set up this test environment together:
➡ We installed a ‘standard’ ActiveDirectory
➡ Two systems were set up with Windows 10 21H1 and two with Windows Server 2019 (Standard) 1809.
➡ The September update was installed on each system.
➡ One Windows 10 and one Windows server computer each had the standard configuration from Microsoft.
➡ The other two systems received a System Hardening configuration based on various recommendations, including deliberately configured deviations.
The test setup was thus as follows:
| w/o system hardening | hardened system | |
| System 1 | Windows 10 | |
| System 2 | Windows 10 | |
| System 3 | Windows Server 2019 | |
| System 4 | Windows Server 2019 |
How was the configuration created?
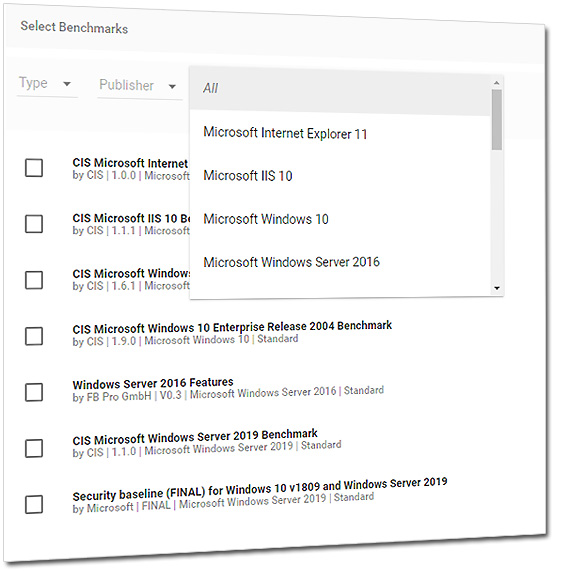
We used the Enforce Administrator to implement the System Hardening and Secure Configuration. The Enforce Administrator offers the option of ‘merging’ several hardening recommendations (the so-called benchmarks) and resolving the conflicts (partially) automatically.
Our hardening configuration for these tests was based on the specifications of CIS, BSI, DISA and Microsoft.
The actual Security Configuration Management – the distribution – is usually role-based and takes place on hundreds or even thousands of target systems. In our scenario, however, there were only the test systems mentioned.
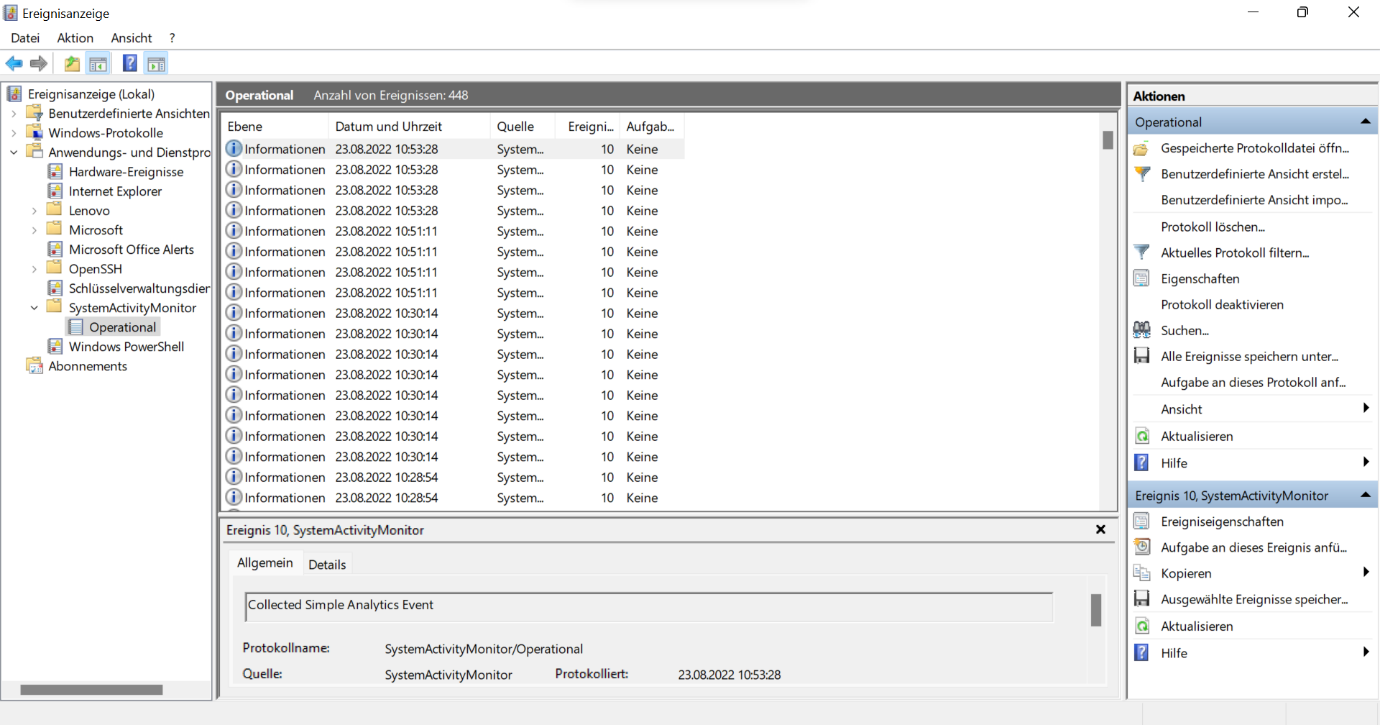
How did we generate the evidence?
The evidence – which is now required by the regulators – can be provided in different ways. For example, by using vulnerability scanners or special tools such as AuditTAP.
For the first test run, Trovent used the Holm Security scanner. This checks hardening conformity based on the specifications of the Center for Internet Security (CIS).
What did the hardening checks show?
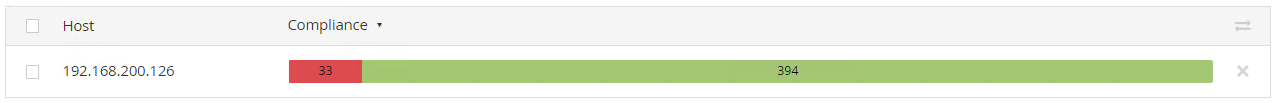
The result was clear: the hardened systems passed significantly more tests than the insecurely configured operating systems!
Here is the evidence:
System 1: Windows 10 without System Hardening
System 2: Windows 10 with System Hardening
And we got these evaluations on the two systems running Windows Server 2019:
System 3: Windows Server 2019 without System Hardening

System 4: Windows Server 2019 with System Hardening
Test round 2: What does System Hardening achieve with Windows 11?
Are newer operating systems configured more securely? Do they even need to be hardened at all? We explored this question in the next test.
To do this, we used two computers with Windows 11 in version 21H2. Each of these systems was scanned once in the unhardened state and once in the hardened state. The systems were hardened again using Enforce Administrator.
For the test, we carried out a ‘Policy Compliance Auditing’ with Tenable Nessus Professional and Holm Security. We also checked the hardening conformity according to the CIS specifications.
As expected, the results were similar to the first check:
System 1: Windows 11 without System Hardening
System 1: Windows 11 with System Hardening
System 2: Windows 11 without System Hardening
System 2: Windows 11 with System Hardening
Test round 3: What does System Hardening achieve in Windows Server 2022?
As part of our third test run, we examined whether modern server operating systems are already configured securely and whether hardening is still necessary. For this purpose, we used Windows Server 2022 21H2.
The System Hardening was carried out in the same way as in the first two tests, with the help of Enforce Administrator. And we again carried out a ‘Policy Compliance Auditing’ with Holm Security to check the CIS benchmarks conformity.
The results were similar to those of the first two checks.
Windows Server 2022 without System Hardening
Windows Server 2022 with System Hardening
Even more tests: Further examples of how well system hardening works
System Hardening is not just about the Secure Configuration of an entire operating system. Restricting individual services can also contribute to greater information security and thus to improved data protection and enhanced privacy.
Stop Windows from being a ‘data octopus’
In one of our numerous tests, we found that an ‘ordinary’ Windows 10 transmits a lot of telemetry data to Microsoft. The Telemetry Monitoring Framework (TMFW) of the German Federal Office for Information Security (BSI) showed that an unhardened Win10 sends data to Microsoft up to 15 times an hour.
A securely configured operating system, on the other hand, remains ‘silent’. As a result, no telemetry data ends up at Microsoft and its partner companies, which include advertising networks. This means that you can ‘stop’ Windows spyware by means of a process known as OS hardening.
No more fear of Mimikatz
The danger posed by pentesting and hacking tools such as Mimikatz can be significantly reduced with a secure configuration. With the right hardening, Mimikatz loses its terror. This is proven, for example, by this German video from our partner TEAL:
Prevent the abuse of SeDebugPrivileges
Would you like another example? In unsecured Windows systems, exploits such as DefenderSwitch and DefenderStop can disable Windows Defender by abusing the SeDebugPrivileges. If these privileges fall into the hands of cybercriminals, it opens the floodgates to all important systems.
In our article ‘How risky are DefenderSwitch and DefenderStop?’, we explain how dangerous such malware tools are. And we show how they can only be stopped with a specially adapted, very strong hardening. Because: Even the benchmarks from Microsoft and CIS were too ‘lax’ in our test and allowed the hacker programs to do their dirty work.
Slow down polymorphic malware
System Hardening not only helps against ‘normal’ malware, but also against polymorphic malware, which constantly changes its code independently! The main danger of polymorphic malware lies in its ability to evade detection by signature-based programs and systems. As a result, the malware usually remains undetected for a long time.
If you configure your operating systems and applications to provide significantly fewer attack surfaces and security vulnerabilities, polymorphic malware becomes less of a threat. This is because with a Secure Configuration, the ‘germs’, which are increasingly based on AI or ML, can only cause little or no damage.
Is it possible to measure the success of System Hardening?
Yes, definitely! As our examples and tests show, the effect of a Secure Configuration can be measured in numbers and with tangible results.
➡ The checks with the tools from Tenable and Holm show that there are significantly fewer security vulnerabilities in hardened systems.
➡ AuditTAP shows how much (or how little) optimisation is needed for an application or operating system according to the hardening benchmarks of well-known organisations.
➡ The check with the BSI’s TMFW proves that Windows stops transmitting telemetry data after good hardening.
➡ (Simulated) attacks, for example with Mimikatz, are unsuccessful because hardened systems offer significantly fewer attack surfaces.
The bottom line is that System Hardening is an excellent preventive cybersecurity measure that, figuratively speaking, locks the doors and windows of a house to make it more difficult for burglars to break in.
Is there 100% protection with System Hardening?
No! Secure Configuration is ‘only’ one of many measures that organisations and companies should take to protect their systems from hackers and malicious attackers. For example, according to the NIST Security Framework, it may be useful to additionally implement an anti-malware scanner, an IDS (Intrusion Detection System) or MDR system (Managed Detection & Response) and/or a SIEM solution (Security Information and Event Management).
Besides the fact that System Hardening alone is not enough to secure your ‘data treasures’, you should also be aware of the following: 100% compliance is extremely unrealistic in the area of hardening as well!
Why you can never fully harden systems
In our opinion, the expectation that a server or workstation operating system or the associated middleware layer can be configured to fully comply with a hardening standard belongs in the realm of security dreams.
System Hardening must always be proportionate and take into account the three protection goals of ‘confidentiality’, ‘integrity’ and ‘availability’. For example, it can be neither sensible nor necessary to configure a system in such a way that access to essential hardware functions and important company data is no longer possible!
For example, current hardening recommendations, such as for Windows Server Hardening or for Windows 10 Hardening, expect, among other things, Bluetooth to be switched off and microphone and camera access to be disabled. However, in times of remote working, home offices and the like, it is precisely these technologies that have to work – for web-based video calls, among other things.
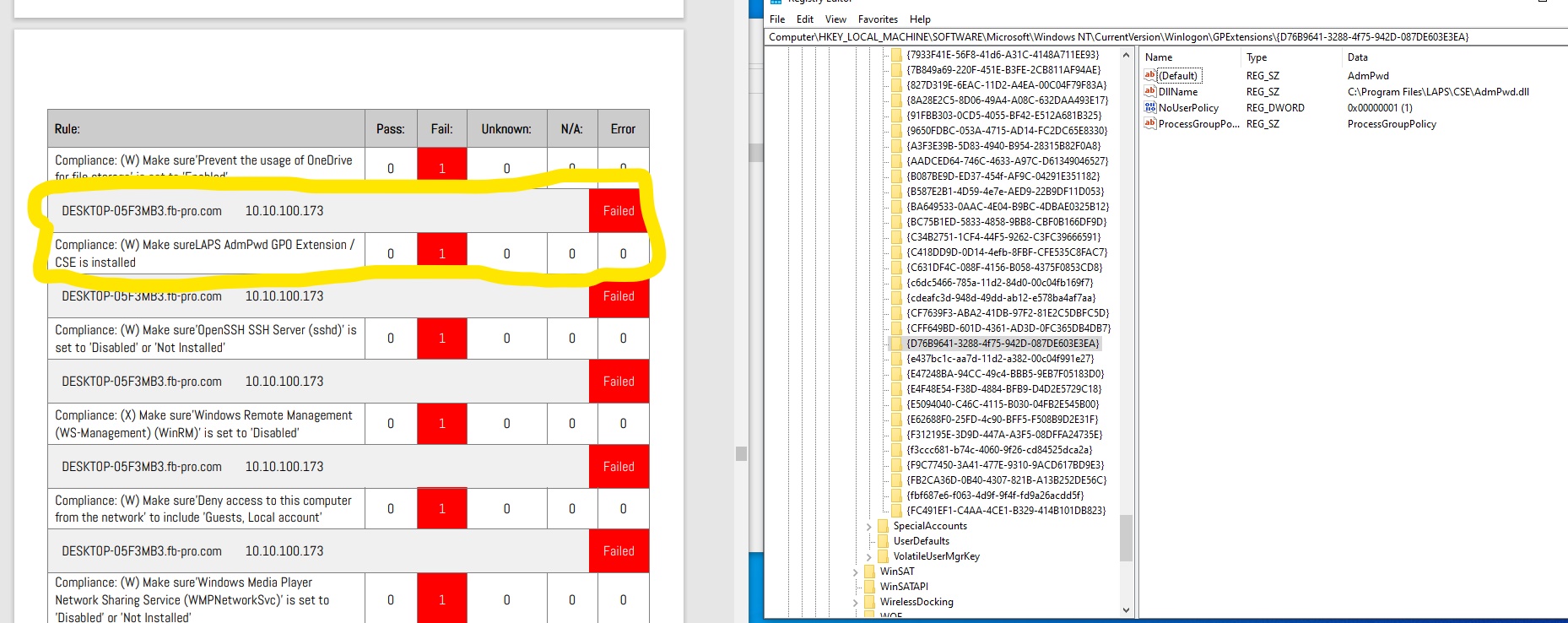
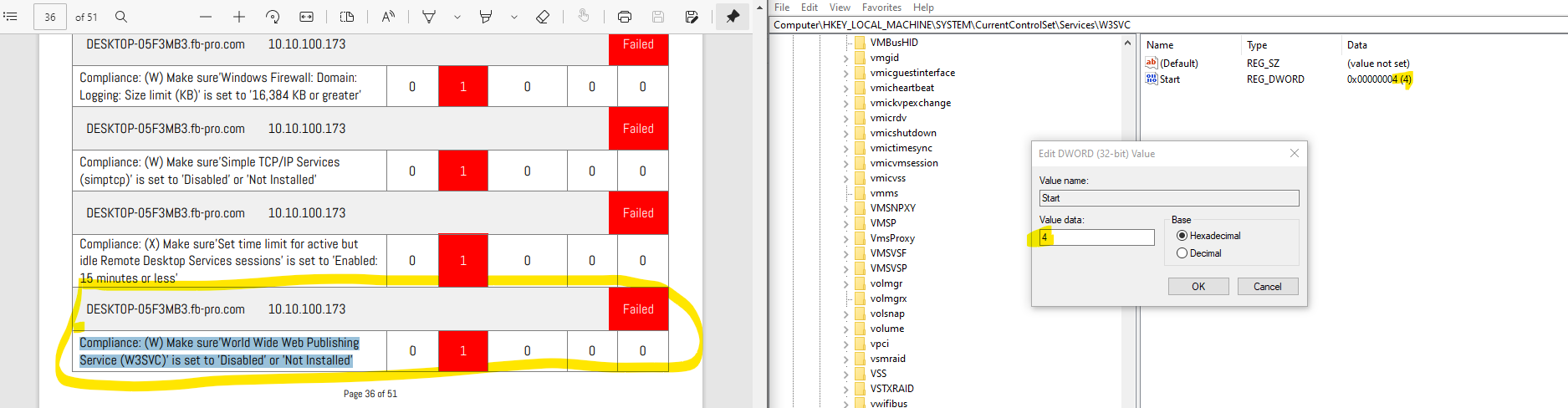
Tip: Remember the ‘false positives’!
You have hardened your systems as much as possible, but hardening tools like AuditTAP still show you numerous suggestions for improvement? This can be a good thing, because some of the supposed ‘FAILs’ fall into the category of ‘false positives’.
This means that the configuration on the system is exactly as it should be, but the hardening report still reports a ‘non-conformity’. Here are two examples:
Example 1: LAPS is actually installed on the test system, as can easily be seen on the right.
Example 2: No web server was installed on our Windows 10 workstation.
Furthermore, Microsoft has a habit of making a parameter configurable in two or more places in its operating systems and applications. So it may be that the system is checked at point 1 but has been adjusted at point 2. In this case, further investigation is required.
The big question: how good is System Hardening really?
System Hardening works! Most systems are configured by default to allow users to get the most out of them – but security usually suffers as a result. Hardening then raises the security level to a higher level.
However, you always have to bear in mind that there is no such thing as a perfectly hardened system! Tests or audits against a hardening standard usually lead to a rather ‘red’ audit report. Often it is even deep red. Why? The individual settings and exceptions for your specifications are often not recorded and role/application-specific adjustments are not taken into account.
A Security Configuration Management solution such as Enforce Administrator makes this easier. In addition to simple configuration, distribution and regular control, it also provides audit reports that take these individual optimisations into account.
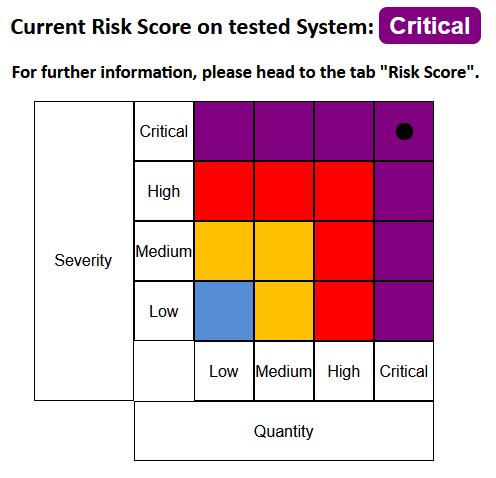
In addition, the AuditTAP displays a risk score. This shows at a glance how critical the settings made are. Here is an example:
Conclusion
Information security, data protection and IT compliance do not work without a specific mix of technical and organisational measures. In addition to infrastructure solutions, the secure configuration of IT systems (hardening) and their updates (patching) are the most effective ways to preventively close vulnerabilities.
The results of System Hardening can be measured and verified in a variety of ways, as our numerous tests and the examples presented in this article have shown. Why not try it out for yourself? You can harden individual applications such as browsers and Office programs, or your entire system landscape. If you need help, our team will be happy to assist you.
Images: Freepik, FB Pro, Microsoft