The AuditTAP offers a practical risk score. This may cause some surprise. We’ll explain how to correctly read and interpret the improved and clear compliance report.
How well are your systems really configured?
Do you know the answer to this question? If not, then you should check your operating system (e.g. Windows 10/11 or Windows Server) or individual applications like MS Office with AuditTAP.
The free tool generates a detailed report on how well you have configured your system according to known hardening standards – or not.
____________
Would you like to know how to install AuditTAP on Windows and use it to perform a hardening audit? This video provides you with many practical tips:
Here’s how to set up AuditTAP on Linux:
____________
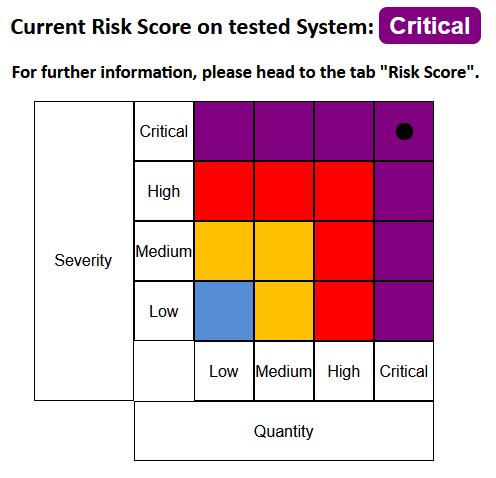
AuditTAP has always offered very detailed views. These show where your audited systems have some catching up to do in terms of System Hardening. With update 5.2 we integrated the Risk Score. This shows at a glance how critical or non-critical the results of your compliance check are.
Is a rating of “critical” really critical? How does AuditTAP arrive at this rating? Which measures should you take and which are better not to take? We will clarify these questions in this article. First, however, we will show the initial situation – because most systems are unfortunately quite insecure by design.
Is a standard Windows well hardened or securely configured?
The clear answer: No!
Microsoft has always delivered Windows with the greatest possible compatibility. This makes many things easier for users. For example, inexperienced private users can quickly and easily connect printers, use expansion cards, install any kind of software or share their game scores via Xbox account.
That means: “ex works” Windows automatically starts numerous services and activates every interface when booting – the functionality could be needed by the user, after all. But this compatibility and ease of use creates a technical attack surface – and thus a high risk for successful cyber attacks.
So a “normal” Windows has relatively little compliance with current hardening standards such as the CIS Benchmarks oer BSI’s SySiPHuS recommendations. Therefore, the summary of the AuditTAP report in this case looks like this:
Also interesting: A standard Windows version doesn’t have much in common with Microsoft’s own security recommendations (the Security Baselines).
This leads to a corresponding risk assessment: The audited system is given the status “critical” in the AuditTAP report.
How exactly does the AuditTAP risk matrix come about?
The AuditTAP Risk Score has two dimensions:
-
- “Quantity”
- “Severity”
Under “Quantity”, the compliance check understands the quantitative match. This means: How many configuration recommendations of the selected hardening standard are configured according to standardized hardening recommendations in the system you are auditing?
The vertical axis of the matrix (“Severity”) ranks the results according to qualitative standards. In other words, how well are the individual configurations implemented on the system you are auditing?
The following examples show you exactly what is meant by this:
Example 1: Quantity “critical” / Severity “medium”

Explanation: In this example, “volume” compliance is critical. But the most important settings have been implemented so well that only a medium risk arises.
Recommendation: Ensure that overall compliance increases. Use the BSI or CIS recommendations. Especially the “L1” settings of the CIS offer a good start.
Example 2: Quantity “high” / Severity “high”

Explanation: Congratulations! You can still make fine adjustments with this result. A deep insight into the individual settings is necessary to bring out the last potential.
Recommendations: A hardening specialist must check and evaluate the Secure Configurations in depth. Among other things, he performs special tests or corresponding checks for this purpose.
🔻 But: Don’t overdo it with System Hardening! Otherwise, your operating systems and applications will be extremely secure, but unusable.
Remember the “Basic Hygiene of Cyber Security”
Before you get started with any System Hardening, you should meet the “basics” of security configuration management. That is, make sure the basic security mechanisms are enabled.
Almost any notebook or desktop hardware today supports crypto chips (“TPM chips”) that provide important basics for standard security functions. Every operating system provides a firewall, use the anti-malware solutions (for example, Windows Defender or another solution) and enable the so-called “Attack Surface Reduction Rules” (ASR rules).
AuditTAP also checks whether you have implemented these basic functionalities. On a Windows system where this “basic hygiene” has been performed, it looks like this:

When performing the following System Hardening, you should always be aware that it is not enough to change only ten or 20 settings!
Role-based hardening based on standards
Are your AuditTAP reports more “red” than “green”? Is the Risk Score sobering? Especially companies have to close the detected vulnerabilities as soon as possible, for example by applying the Microsoft Security Baselines and a professional Windows 10 hardening!
➡ There are now various, comprehensive standards that you can use as a guide. For example, BSI, DISA, CIS and the ACSC regularly issue new recommendations. These include several hundred settings that should be applied to harden Windows, for example.
➡ If you combine several standards and also include individual applications such as office suites and browsers in your hardening, 1,000 adjustments and more quickly add up.
➡ If you want to close these vulnerabilities manually – and on dozens or even hundreds of systems – you’ll have your work cut out for you. It’s better to do the secure configurations with hardening tools like Enforce Administrator.
➡ But don’t go overboard with hardening! The benefit of System Hardening is great – but you may overshoot the mark. Always keep these three protection goals in mind:
-
- Confidentiality
- Integrity
- Availability
Do you need help with the secure configuration of systems?
Do you have questions about AuditTAP? Or do you need support with (automated) System Hardening? Do you want to integrate System Hardening directly into your deployment or installation processes? Our experts are here for you! Contact us without obligation and we will get back to you as soon as possible.
Images: Smartmockups.com, FB Pro