A new tool from the German Federal Office for Information Security can be used to check how much telemetry information an unsecured Windows 10 or Windows 11 sends to Microsoft. We tried it out and came up with some astonishing results.
Important: Limit Microsoft’s “hunger for data”!
What do E.T., Windows 10 and Windows 11 have in common? All of them would like to phone home. But in the case of the operating systems, “phoning home” is not a good thing. Microsoft itself justifies the collection of data with the fact that applications should work “trouble-free and securely”.
German security authorities (such as the Federal Office for Information Security, called BSI) and security experts see things differently: user and usage data is collected, which makes the use of applications and thus ultimately the users more transparent. This is precisely what the General Data Protection Regulation (GDPR) is designed to prevent. The principle behind this is called “data minimisation“.
The fact that a Windows 10/11 “ex works” sends quite a lot of data “home” is no secret. Thus, it was always clear that the company from Redmond has an interest in the telemetry data of its users. These are automatically stored in an unconfigured or even rudimentarily configured Windows, afterwards sent to Microsoft servers and evaluated there.
But how much information does an activated telemetry service collect? That can now be found out with a new open-source tool – the System Activity Monitor (SAM) – from the BSI.
From a Sisyphean task to telemetry monitoring
The BSI has been investigating the new Microsoft operating systems with cooperation partners for many years. As part of SiSyPHuS (Study on System Design, Logging, Hardening and Security Functions), new findings regularly come to light. From this, the BSI derives, among other things, important suggestions on how you can make Windows 10 more secure. Unfortunately, there is currently no really reliable information for Windows 11.
A rather fresh publication is called Telemetry Monitoring Framework (TMFW). In the document, which is over 30 pages long BSI explains how to use the System Activity Monitor (SAM). SAM is a free tool to examine the recording profiles of Windows 10 and Windows 11.
This means that it becomes transparent in Windows’ own event log how often and how much data the Windows telemetry service collects in order to send it to Microsoft servers.
How to start the System Activity Monitor?
SAM can be found on the official BSI page (direct download here as a ZIP file), the source code is available on Azure DevOps.
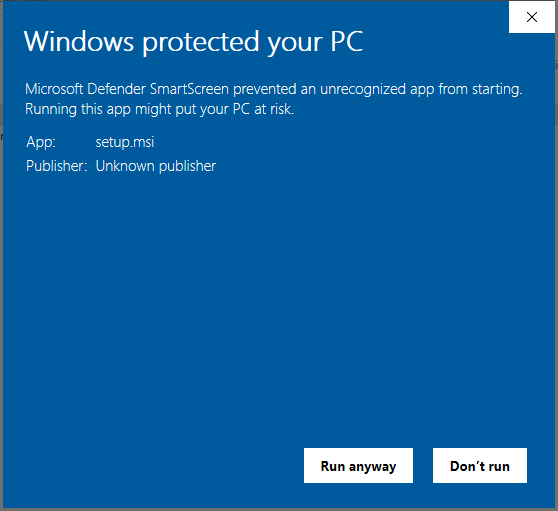
The tool is installed like any other Windows application. However, there is a warning in between that you have to read briefly and then confirm. The tool is not signed, and the Windows function “SmartScreen” therefore brings up a warning.
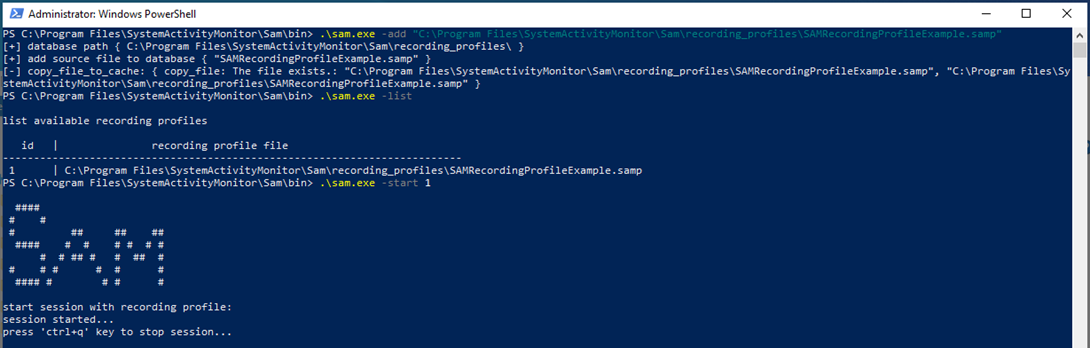
After you have installed the tool, you need to add a recording profile. We simply used the provided file “SAMRecordingProfileExample.samp ” for this purpose.
Using the Powershell command “.\sam.exe -list” you can see the list with the recording profiles and the corresponding IDs. Select number 1 – and off you go!
Tip: Click on the blog images to see them full size.
How much data the Windows 10 telemetry service really sends to Microsoft
Are the telemetry features of Windows 10 and Windows 11 really as bad as their reputation? We have checked.
The test setup
For our test, we installed SAM on several equivalent notebooks. These were four fully patched Lenovo ThinkPads, two with Windows 10 and two with Windows 11.
All notebooks had an unrestricted Internet connection, and no filtering measures were implemented at the network level. For this, we hardened two systems.
The configuration used was an amalgamation of various hardening specifications (from BSI and CIS, among others). We compiled these and configured them using the Enforce Administrator hardening tool. Since the BSI has not yet issued updated recommendations for Windows 11, we used the Windows 10 hardening recommendations throughout.
The test setup then looked like this:
| Windows 10 incl. August patches | Windows 11 incl. August patches | SAM tool installed | Hardening configured | |
| System 1 | X | X | ||
| System 2 | X | X | X | |
| System 3 | X | X | ||
| System 4 | X | X | X |
During our test, we continued to work with all four test systems as normal for about a week.
The evaluation of the results
What did our test reveal? You can see the results in this table:
| Windows 10 w/o hardening | Windows 10 hardened | Windows 11 w/o hardening | Windows 11 hardened |
|
|---|---|---|---|---|
| Data transmission detected | Yes | No | Yes | No |
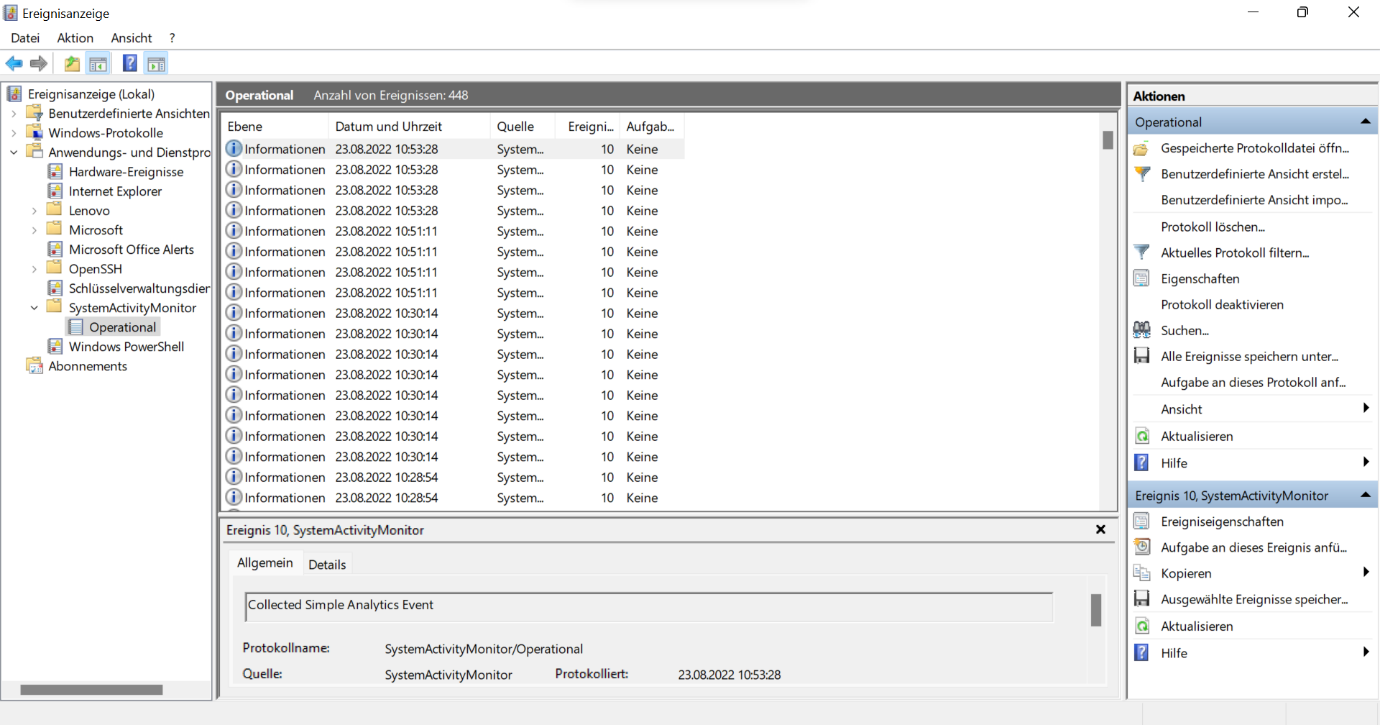
The unhardened Windows 11 system sent 448 data packets to Microsoft in one week. Here is an excerpt as a screenshot:
The Windows 11 with System Hardening, on the other hand, remained “muted”, not a single transmission of telemetry data occurred.
We got similar results on the two Windows 10 devices: While the hardened notebook did not transmit any information to Microsoft, SAM showed a lot of “radio traffic” on a Windows 10 without System Hardening. In some cases, data was sent up to 15 times per hour!
How should you act now?
As expected, the telemetry service of an unhardened Win10/11 system transmits lots of data. How exactly this data is handled and what exactly is contained in these encrypted data packets is unclear as of today. Microsoft can use this data, for example, to find out more about you. Whether you want that as a private person is up to you.
However, the GDPR obliges companies to be economical with data. Only as little data as possible may be transmitted to third parties.
Our recommendation: Turn off the telemetry services of Windows 10 and Windows 11 ! In this way, you actively reduce the liability risks according to GDPR
Additionally, it is a must to use hardening tools to achieve continuously secured and robust systems. This will automatically disable the telemetry service and other unnecessary but data-hungry functions. Otherwise, information can flow out unintentionally – about your employees, about your company and possibly about your customers.
In addition, unhardened systems are an easier gateway for hackers and other cyber criminals. They exploit vulnerabilities that exist through systems in default configurations, among other things. This makes it far too easy for attackers to infiltrate espionage tools and malware. This can quickly lead to consequences that result in high and expensive damage.
How can System Hardening be implemented?
First of all, a status quo must be determined: How well are the existing systems currently hardened? The result can be found out with the open source and free of charge AuditTAP.
Once it is clear what the status is in terms of secure system configuration, the next step is to get better. That means you have to perform System Hardening. And measures must be taken to maintain hardening permanently and fully automatically. This is possible, for example, with the Enforce Suite.
Do you need support with System Hardening? Our team of System Hardening experts will be happy to provide you with advice and support. Contact us for a no-obligation inquiry!
Images: Freepik, Microsoft, FB Pro