There is a fresh update for the AuditTAP! You can now check even better whether your systems are securely configured (“hardened”) to the state of the art. Additionally, current project requirements are implemented.
[lwptoc min=”3″ depth=”1″ title=”Table of Contents:”]
AudiTAP – always on the pulse of time
IT security is not a project with a fixed end. And it is also not a sprint, but rather a marathon. It is therefore important to stay on top of the topic, constantly and without interruption.
That’s why we are continuously improving AuditTAP (ATAP for short), among other things. In version 5.5, we have implemented a few new functions to keep you “up to date” in cyber security.
The biggest changes in AuditTAP
As a reminder: According to the state of the art techniques, only TLS 1.2 or higher is to be used. We have implemented these and other checks in the new AuditTAP. This makes it easy to see which SSL/TLS protocols are active.
In addition, AuditTAP 5.5 for Windows Server 2022 supports the DISA STIGs (Security Technical Implementation Guides) in version V1R1 and checks systems with Windows Server 2012 R2 according to the new CIS Checks 2.6.0, among others.
In addition, we have added tests for “stand-alone” Windows systems that are not members of an Active Directory domain. The basis for these checks are CIS and BSI recommendations
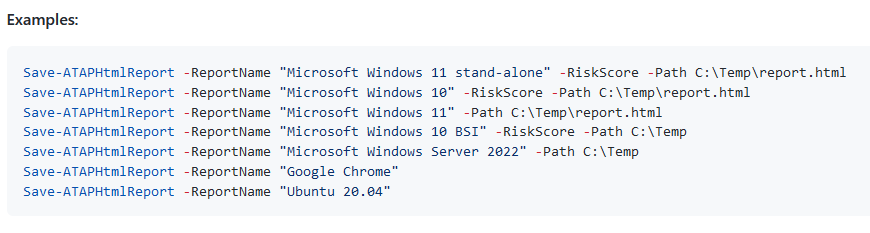
How exactly a hardening report is generated for these systems is documented here. The following screenshot shows a selected example:
All the existing as well as the new checks have an impact on the calculation of the AuditTAP Risk Score. This shows in an easy-to-understand presentation whether there are critical weaknesses in your system hardening or not.
Hardening recommendations away from CIS, DISA & Co.
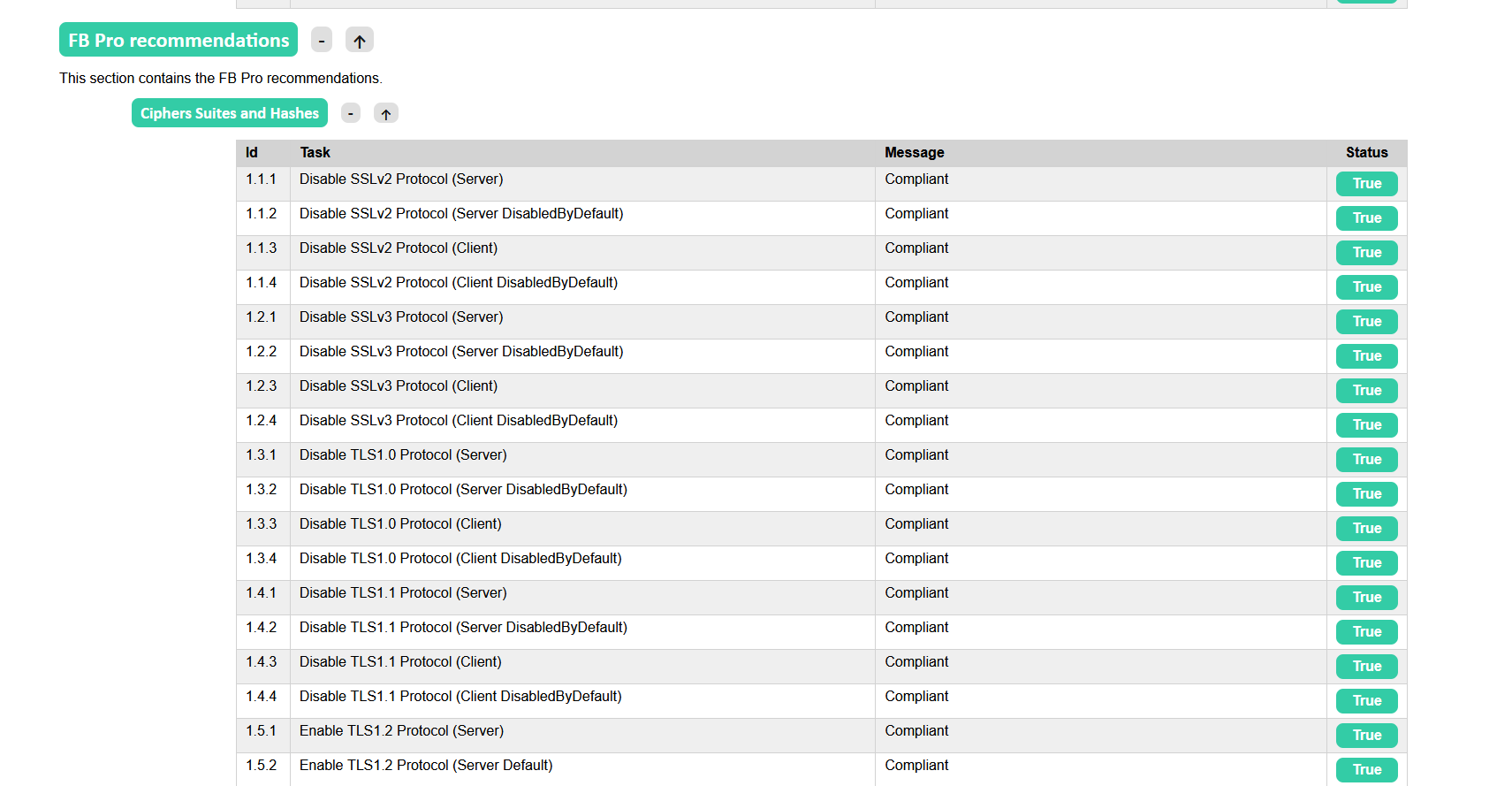
Another fresh feature is called “FB Recommendations”. With this, we perform special tests that are not based on the recommendations of CIS, DISA, BSI, ACSC and Microsoft. Instead, AuditTAP checks your Windows 10, Windows 11, and/or Windows Server system for configurations that we recommend as a supplement to the known standards.
The “FB Recommendations” function can be found in the “Hardening Setting” tab. A result may then look like this in the section, for example:
Customer request for the next version leap
With version 5.5, a special feature moves in that has resulted from customer projects in which AuditTAP is actively used.
The challenge
In a highly regulated environment, the integrity status of an IT system must be verifiably documented, even over a longer period of time. AuditTAP has been able to generate reports for quite some time, and the use of generated reports as evidence / proof in audits by auditors is more or less common practice.
But: A comparison of several AuditTAP reports was not so easily possible until now.
The solution
In the area of “Hardenig Settings” we have implemented a hash value calculation on project request. This calculates a unique hash value for all controlled settings. If several reports are now generated over a period of time, it is possible to check whether there have been changes in the more than 1,000 controlled settings by reading a hash value. If the hash value remains unchanged, the settings are identically configured.

What else is new?
Bugfixes, bugfixes and bugfixes. You can see a list of all closed issues on GitHub.
Among other things, our “exterminators” fixed bugs in the DISA tests for Windows Server 2019 and incorrect information in the Windows Defender checks. They also adjusted the logic of some checks and revised the test names to avoid misunderstandings.
Would you like to participate in the improvement and further development of AuditTAP yourself? Then submit your suggestions here.
Do you have any questions about AuditTAP? Or do you need support for (automated) system hardening? Then get in touch with us without any obligation by sending us an e-mail.